Proven Results in Finance
$2.5M
Saved in Annual Fraud Losses
$150k
Reduced Year-1 Admin Spend
$500k+
Avoided in Fines + Audit Fees
Protect Access Across Your Entire Manufacturing Ecosystem
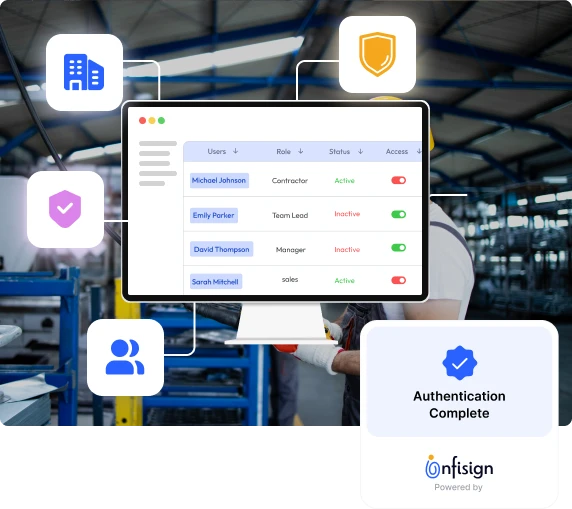


Why Choose Infisign for Manufacturing Access Management Across Sectors

Manage complex global partner networks efficiently. Secure access across tier-1 and tier-2 suppliers in the transportation industry to prevent critical production delays and protect proprietary vehicle designs.

Maintain strict regulatory compliance and traceability. Track workforce and contractor access across food and beverage facilities to ensure only certified personnel interact with sensitive production equipment.

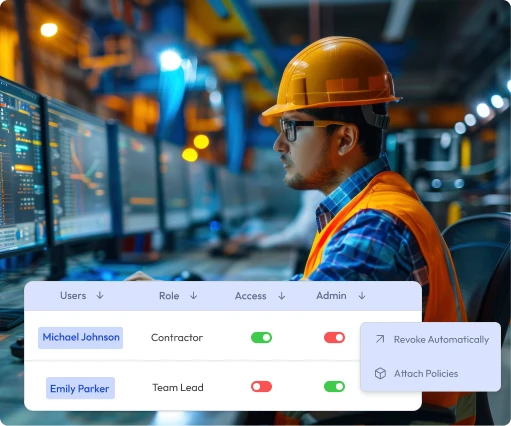
Control non-human identities on the factory floor. Assign and manage secure access policies for interconnected operational technology across metal, electronics, building materials, and machinery production lines.

Create rigorous access controls in hazardous environments. Use identity management to restrict sensitive system access within rubber, plastic, and chemical plants, ensuring safety and operational integrity.

Streamline identity management for high-turnover shift environments. Enable fast, phoneless authentication on shared shop-floor terminals for workers in textiles, apparel, and accessories manufacturing.
Regulatory Compliance and Certifications

Deployment Environments for Infisign

On-Premise
Deploy Infisign within your secure data center for maximum control, integrating directly with local AD or LDAP infrastructure

Multi-Directory and Tenant-Cloud
Unify disparate identities from acquisitions and partners, syncing seamlessly with external providers like Auth0, Okta, and Azure AD.

Private Cloud and Hybrid
Bridge legacy banking systems with modern SaaS apps via standardized SAML and OIDC protocols, for hybrid compatibility.
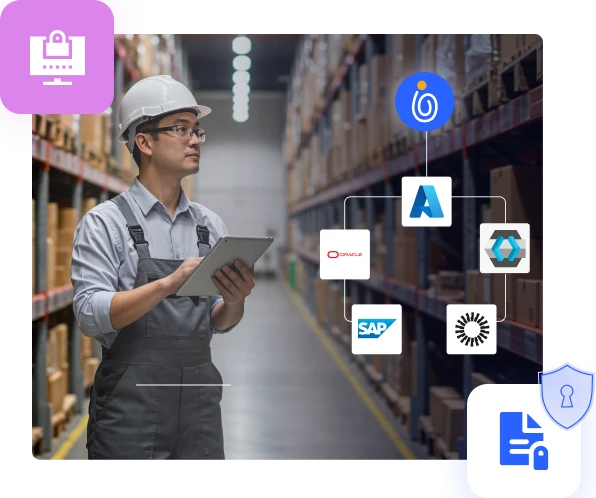
Compatible with All Financial Solutions

Citrix
.svg)
Workday

Office 365

ServiceNow
.svg)
Caller Verify

SAP
.svg)
Oracle

Salesforce
Health Cloud
.svg)
Cerner

Netsuite
FAQs on Healthcare IAM




FAQs on Manufacturing Access Management Software











































