End Password Chaos and Identity Theft With Biometric Authentication

Features That Make Our Privileged Access Management Better

Automated Granular Access on Application Level


Secure and Encrypted Access With SSH, RDP, and PemKeys
.webp)
Zero-TrustBiometric Authentication Mechanismswith Infisign



Why is Infisign the Right Fit for More Reliable Security?
Add SSO to On-Premises Only Applications

Works With Non-SSO Compatible Software

Reduce Manual Updates With Automation
New hires get instant access, and former employees lose it the moment they leave.
Use With On-Premises, Cloud, and Hybrid
From legacy systems to the latest SaaS tools, secure access to everything without disrupting workflows.
Avoid Fines With Instant Audit Readiness
Track every login and change in real-time with reports when you need them. Stay ahead of compliance checks
Keep Accounts Safe With Brute Force Protection
Block automated login attempts before they even start. Keep your apps and users safe from credential-stuffing attacks.
Complex Regulatory Compliance (GDPR, HIPPA, BIPA, CCPA)
We verify identity using Zero-Knowledge Proofs, making sure to never store raw biometric data. Eliminate the risk of the US and EU privacy mandate breaches.

.webp)
Create Better Security With Conditional Access




Just-In-Time Access for Employees + Vendors


Stay Auditable and
Compliant With
Audit Logs

Benefits of Using
Infisign’s PAM Solution

Remove Access Creep
Infisign PAM actively prevents the accumulation of unnecessary access rights, tightening your security and removing access creep.

No More Risks of Compliance Fines
Create better access control with the audit trails necessary to avoid penalties and demonstrate due diligence.

One Unified Access for Multiple Access Directories
Centralize privileged access management across all your IdP directories with complete visibility on which partners, vendors, and distributors have access to what.

Stop Data Breaches With Passwordless Authentication
Secure logins with OTPs, biometrics, and QR codes. No passwords means no phishing or credential attacks.

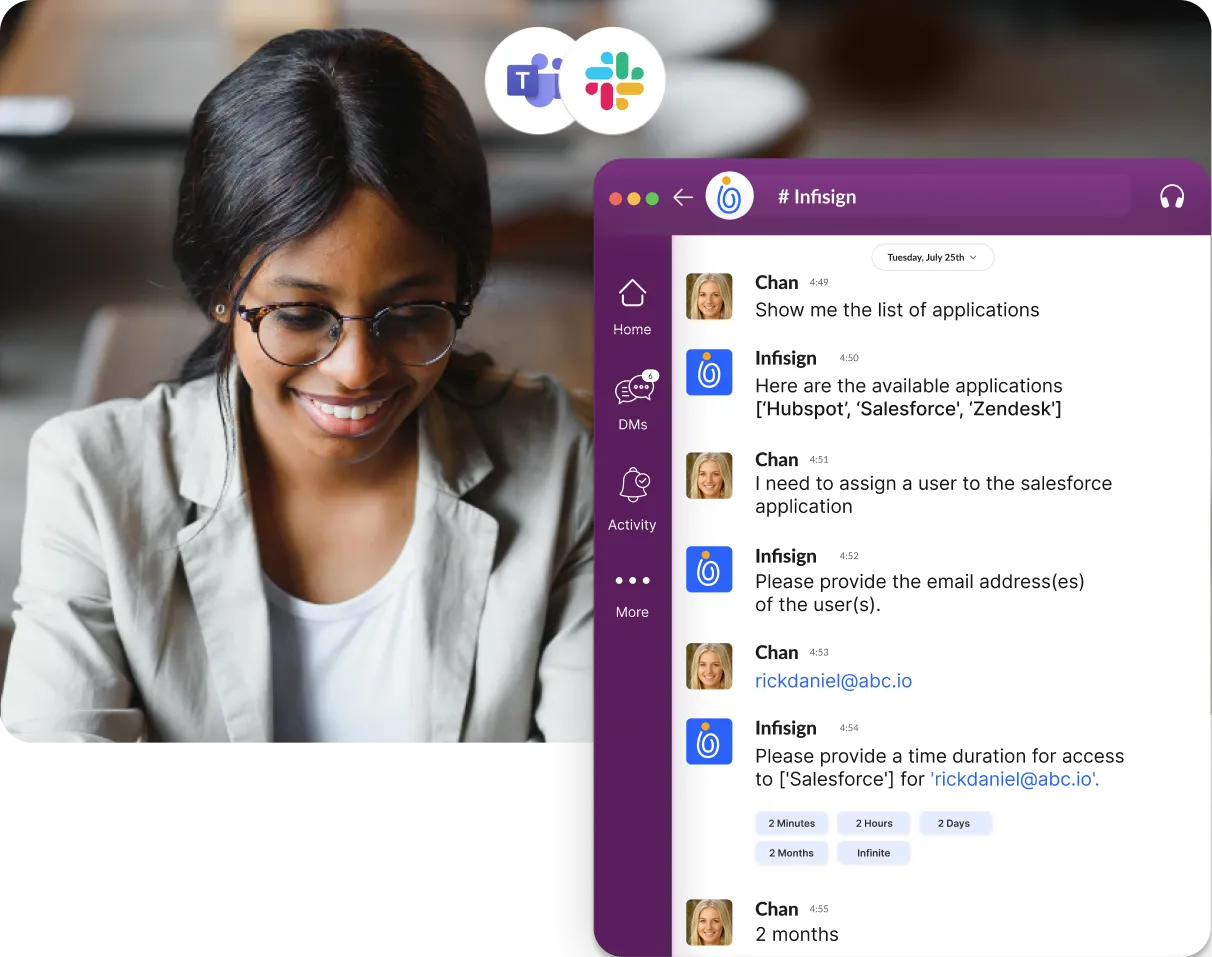
Lower IT Overhead With AI Access Assist
Lower costs with AI-access assist that makes granting access quicker and easier, and without the privileged access support tickets.

Stop Password Oversharing
Stop the pointless risk of sharing privileged credentials. Secures and manages access without exposing sensitive passwords with Infisign.

Remove Security Gaps in Legacy and Web-Based Apps
Add protection across your entire application landscape, no matter the application! Add passwordless authentication to apps that do not support modern access control.

Stop Data Breaches With Passwordless Authentication
Secure logins with OTPs, biometrics, and QR codes. No passwords means no phishing or credential attacks.
Connect Instantly With Over 6000+ Pre-Built Integrations

Azure

Google Workspace

Github

Gitlab

Tableau

Asana

Atlassian

Salesforce

Zoominfo

Netsuite
Secure Access at
Every Ecosystem You Use

Instant Cloud Deployment
Deploy biometric authentication solutions via SaaS instantly. Get global scale without managing infrastructure.

Complete On-Prem Control
Keep all data in your environment. Ideal for air-gapped networks and total data sovereignty.

Flexible SDKs + API-First Flows
Embed unforgeable biometric authentication software into any app. Use our SDKs to build custom, secure user journeys.
Why Infisign Biometric AuthenticationBeats the Competition
Modify access provisioning quicker, detect issues instantly, and eliminate some of the IT support bottlenecks that come with roles.

Create dynamic rules for your biometric solution that trigger authentication only when accessing sensitive files or performing critical administrative tasks.

Destroy silos by unifying physical doors and digital logins into one seamless platform. Eliminate the security risks of shadow IT and access gaps.

Secure and encrypt every SSH, RDP, and PemKey connection. Stop attackers from owning your infrastructure.

Silence the auditors by generating immutable, forensic-grade logs for every action. Prove exactly who did what with absolute certainty.
Get Adaptive PAM Security That's Fast & Passwordless
OTPs
Skip passwords altogether with OTPs, QR codes, push notifications, and magic links. Say goodbye to ransomware and credential stuffing.

Social Login
Improve employee experience and time wastage using popular social logins like Google Workspace or Microsoft with fast and familiar access.
%20(1).webp)
Biometrics+Device Passkeys
Enable the use of Face scans, fingerprints, or device-based passkeys— good security should be effortless.
.webp)
Managed Password Login
For apps that don’t support SSO, securely store and autofill passwords without ever exposing them. Have 360-degree control for even non-sso-compatible applications.
.webp)
FAQs on Biometric Authentication Solutions





Ready to Eliminate Credential Theft?
One Identity Platform for Your Entire Workforce










.webp)














