Growth often looks like more traffic, more users, and more channels. In reality, growth usually tests identity first. When access feels slow, confusing, or repetitive, customers lose patience before they lose interest.
Social identity providers help remove that friction by letting users enter through identities they already trust. Used well, they can improve conversion speed and continuity. Used poorly, they can create dependency, complexity, and future limits.
What Social Identity Providers Actually Handle
Social identity providers help users sign in with trusted accounts like Google or Facebook. They support onboarding and provide limited identity signals that help create a smoother first user experience. However they should not be treated as complete identity verification or fraud assurance.
They Reduce First Step Resistance
The first decision a user makes is whether joining feels worth the effort. Long forms, new passwords and unnecessary fields create hesitation. Social access lowers that mental cost.
As Wipro Director Praveen Nallapothula notes in his discussion on silent authentication, modern identity systems are increasingly designed to reduce friction without removing the user’s sense of trust, visibility, and control during authentication journeys.
- Faster account creation. Users can enter with accounts they already use daily. This shortens the path between interest and action. Less effort often means more completed signups.
- Lower password fatigue. Many people are tired of creating and remembering new credentials. Existing identities remove one more burden. Simplicity can quietly improve conversion.
- Stronger early trust. Known brands create familiarity during entry. That familiarity can reduce uncertainty in the first moments. Comfort matters more than many teams realize.
They Pass Trusted Identity Signals
Modern identity is not only about usernames. It also includes signals that help systems understand legitimacy and reduce abuse. Social IdPs can provide useful context when businesses use those signals carefully and responsibly.
- Verified profile data. Email status, names, or profile basics may arrive from trusted sources, depending on permissions. This can improve onboarding quality.
- Reputation indicators. Older active accounts often feel more trustworthy than brand new identities because patterns build confidence over time. Provider-issued claims can support risk decisions but strong systems also check device behavior velocity and fraud signals before building trust.
- Risk support. Identity signals can complement fraud checks during signup or login. One source should never decide everything. Combined evidence creates stronger decisions.
They Depend on Standard Protocols
Behind every clean login button sits structured identity exchange. Strong architecture matters because convenience without standards creates future pain. This is where OAuth 2.0 authorization, OpenID Connect authentication and modern federation models become important.
- Delegated access flows. Users approve access without sharing passwords directly with your platform. That separation improves security design. Boundaries matter.
- Token based trust. Applications receive tokens instead of raw credentials which creates cleaner and safer system interaction. Trust should never come from the token alone. Good systems validate tokens first before accepting claims or granting access.
- Portable integrations. Standards make it easier to connect multiple providers over time. Flexibility today protects choices tomorrow.
Where Social Identity Providers Break Under Growth
What works at a small scale may create strain later. Many teams celebrate early signup gains but ignore operational complexity that arrives with expansion. Growth exposes every shortcut eventually. Identity architecture should be judged not only by launch speed but by durability.
Many organizations still lack centralized visibility across their identity environments, creating governance blind spots and fragmented identity control as systems and integrations scale.
Too Many Providers Can Create Disorder
Adding more social identity providers can look like progress. Yet each provider brings policies, APIs, metadata, edge cases, and support demands. Convenience can become fragmentation if identity growth is left unmanaged.
- Inconsistent user journeys. Different providers may return different data fields, consent flows and recovery experiences. Customers notice uneven experiences quickly.
- More maintenance overhead. Every new connection needs updates testing monitoring and governance. Small additions often create long obligations.
- Duplicate identities. One user may register through different providers over time. Without account linking identity records become messy. Messy identity weakens decisions.
Provider Dependency Creates Strategic Risk
External platforms change rules, prices, and capabilities over time. When identity depends too heavily on a few social IdPs, business flexibility becomes harder to protect. Mature teams plan early so future growth stays adaptable and stable.
- Policy changes happen. Scope permissions branding rules or API behavior can change with limited notice. Your roadmap then depends on someone else. Dependency has a cost.
- Regional availability differs. Some providers are stronger in certain markets than others. Global growth often needs broader thinking. Local habits matter.
- Outage exposure exists. If one provider fails access journeys may suffer. Resilience should be designed before incidents occur.
Growth Needs More Than Social Login
Social entry can help acquisition yet it cannot solve every identity need. Mature platforms need stronger control across lifecycle governance and customer relationships. This becomes critical in B2C identity management.
- Consent management expands. Businesses must manage permissions, privacy choices and changing regulations. Social login alone does not complete that responsibility.
- Lifecycle complexity grows. Account linking recovery preference control and risk based authentication become more important over time. Real identity work begins after signup.
- Business ownership matters. Customer identity should remain a business asset not only a third party dependency. Long term control creates leverage.
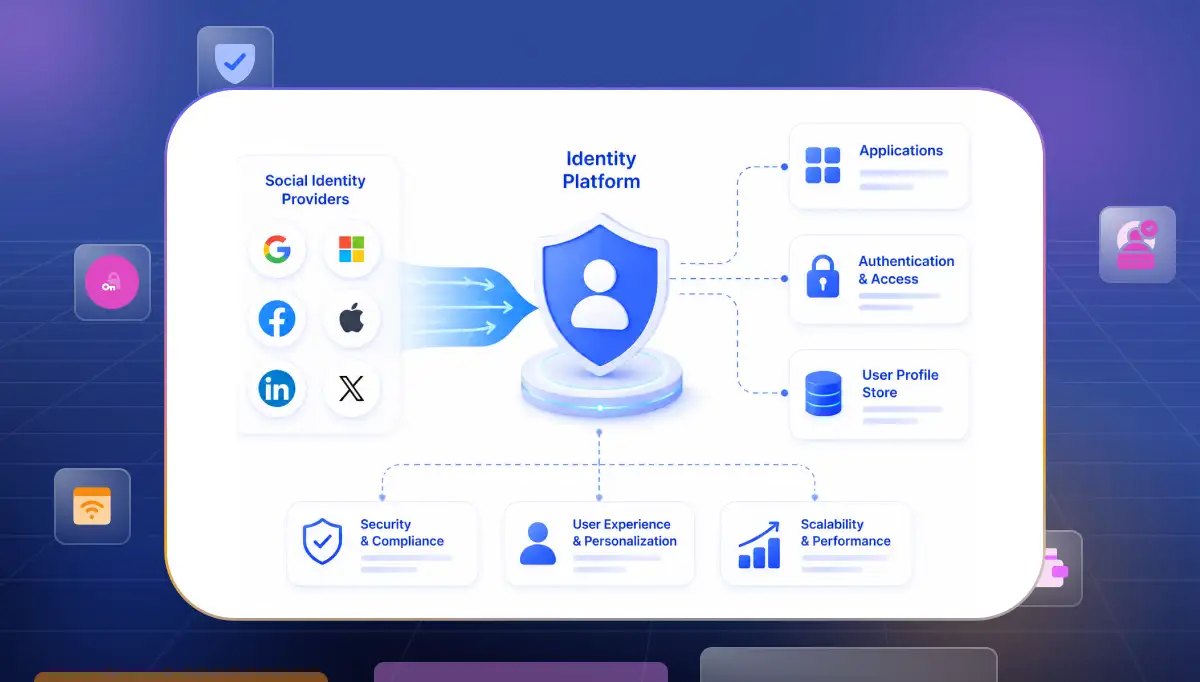
What a Scalable Identity Architecture Looks Like Around Social IdPs
Strong architecture uses social providers as one layer not the entire foundation. The goal is flexibility control and smooth customer experience together. External identity should plug into your system not define your future. This is where thoughtful design separates fast launches from lasting platforms.
Use an Identity Hub Model
Instead of connecting every app to every provider directly, smart teams centralize identity logic. One core layer handles federation policies profiles and governance. Simplicity at the center reduces chaos at the edges.
- Single control point. Policies branding risk rules and provider logic can be managed in one place. This improves the speed of change. Central clarity saves time.
- Cleaner application design. Apps connect to one identity layer rather than many external providers. Engineering becomes lighter. Focus returns to product work.
- Better reporting visibility. Authentication journeys and provider performance become easier to measure. What is visible can be improved.
Keep Standards at the Core
Architecture ages better when built on open standards instead of custom shortcuts. This is why many teams prioritize OpenID Connect identity providers when planning federation at scale.
- Consistent authentication flows. Standard claims and token models reduce custom exceptions. Order improves maintainability.
- Faster provider onboarding. New providers become easier to add when the core model is already structured. Good preparation creates speed later.
- Future portability. Standards reduce lock-in pressure over time. Freedom is strategic.
Own the Customer Relationship
External identities may help with entry but your platform should own the lasting customer profile. That includes preferences, linked accounts permissions and lifecycle controls.
- Unified customer records. Data from multiple providers should map into one durable profile. Customers should feel recognized, not fragmented.
- Independent policy control. Your rules for security consent and journeys should remain yours. Ownership protects agility.
- Stronger long term trust. Users trust brands that feel stable and organized across time. Identity continuity creates that feeling.
Social Identity Providers Worth Considering for Scale
Choosing a provider is rarely only a technical decision. A strong CIAM solution affects launch speed, operating cost, customer experience and long term flexibility. Some tools feel simple early but become restrictive during growth.
Others need more planning yet support scale more naturally. Based on implementation ease pricing practicality and business flexibility these options deserve attention.
Infisign UniFed
Many growing teams need one platform that balances speed, control, and cost discipline. Infisign UniFed supports social providers like Google, Microsoft, Facebook, GitHub, and X, which helps businesses create faster and more familiar login experiences for users.
It fits organizations that want modern federation without enterprise level complexity too early, while still keeping room for future growth and structure.
- Fast implementation path. Teams often value solutions that reduce setup friction and shorten time to launch. Faster execution creates earlier business returns. Speed matters when growth windows are open.
- Practical pricing logic.Growing businesses need identity systems that remain manageable as user volumes expand. Infisign UniFed supports scale with flexible pricing and operational simplicity, helping teams grow without adding unnecessary complexity or unpredictable cost pressure.
- Unified identity direction. Infisign UniFed brings social logins, enterprise IdPs, and external access into one simple system. As businesses grow, one clear login experience creates better control, easier access, and stronger operational clarity.
Auth0
Auth0 is widely known for developer friendly identity deployment and flexible integrations. Many product led teams choose it when speed and customization for social identity providers matter most. It remains a popular choice for modern digital products.
- Strong developer experience. Good documentation and broad ecosystem support can reduce implementation drag. Engineering teams often value this highly. Smooth starts matter.
- Flexible extensibility. Custom flows, rules and integrations are possible for many use cases. This helps teams shape identity around product needs. Adaptability creates room to grow.
- Well recognized market presence. Mature vendor presence can create confidence during buying decisions. Reputation sometimes shortens internal approval cycles.
Okta Customer Identity
Okta Customer Identity is often considered by enterprises that need governance scale and broad security alignment. It can suit organizations with larger programs and more layered requirements. Mature environments may value its ecosystem strength.
- Enterprise readiness. Larger companies often need advanced controls reporting and cross team governance. Structured platforms can support that complexity. Discipline matters at scale.
- Security alignment. Businesses already using Okta internally may prefer vendor consistency. Operational familiarity can reduce friction. Known systems lower learning curves.
- Scalable architecture options. High volume customer environments need resilience and performance planning. Established platforms often invest heavily here.
What to Evaluate Before You Add More Providers
Adding providers can improve reach but unmanaged expansion creates identity debt. Each new connection affects support governance analytics and customer journeys. Smart teams evaluate long term impact before chasing short term convenience.
User Demand Before Feature Demand
Not every requested provider deserves implementation. Some requests are loud but low value. Decisions should follow real user behavior.
- Regional relevance. Some social identity providers are trusted more in certain markets. User habits often matter more than assumptions. Geography strongly influences how people choose to sign in and engage with digital platforms.
- Audience fit. Consumer users, students , gamers professionals and enterprise buyers may prefer different identity choices. Context matters more than trend chasing.
- Measured demand. Surveys funnel data and abandonment patterns reveal genuine need. Evidence prevents waste.
Operational Cost Behind Every Integration
Every provider adds more than a button on a page. It adds ownership responsibility and maintenance.
- Ongoing updates. APIs, scopes, certificates and policies can change over time. Someone must monitor that reality. Neglect becomes a risk.
- Support complexity. Login issues may vary by provider device or browser. More options can mean more edge cases. Simplicity has value.
- Testing burden. Each release may require broader regression testing across identity flows. Hidden work accumulates quietly.
Strategic Control and Exit Options
The best identity decisions preserve future freedom. Convenience today should not trap tomorrow.
- Portable architecture. Strong social IdP integration should happen through a central layer not hard coded across many apps. Portability reduces future pain.
- Data ownership clarity. Customer profiles preferences and linked accounts should remain under your control. Ownership supports leverage.
- Fallback readiness. If one provider changes terms or fails operations alternatives should exist. Resilience is strategy.
Getting Social Identity Providers Right From the Start
Identity decisions made early often stay with a business for years. Fast signup feels exciting in the beginning but scattered systems become difficult to manage later. Strong identity design gives businesses speed today and stability as they grow.
Customer Trust Begins With Structured Access
People trust systems that feel clear, familiar, and easy to return to. When identity stays organized, users face less confusion and businesses face less operational disorder. Trusted social providers, consistent experiences, and reliable recovery paths create a stronger relationship between access and confidence.
Grow Without Losing Clarity
Growth brings more users, more providers, and more complexity. Platforms like Infisign UniFed help businesses manage social login, passwordless access, and identity flows in one place, so expansion feels organized instead of difficult.
If your business is planning growth, expansion, or a cleaner customer login experience, exploring Infisign UniFed is a practical next step. Book your demo today!
FAQs
What is the difference between social identity providers and enterprise identity providers?
Social identity providers focus on consumer accounts such as Google , Apple, or Facebook, used for customer access. Enterprise identity providers usually manage workforce or partner access through corporate directories and business policies. One serves public user convenience while the other often serves organizational control.
How do social identity providers fit into a CIAM architecture?
They usually act as external authentication sources connected into a central CIAM layer. The platform then manages user profiles, consent, security policies, account linking, and customer journeys. This approach keeps social login simple for users while helping businesses maintain stronger control.
How do you handle consent management with social login?
Consent should be separated into two layers. First the user approves data sharing from the provider. Then your platform should manage its own permissions preferences and privacy controls clearly. Trust improves when both steps are transparent.